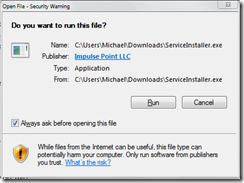
I show up for a meeting, flip open my netbook and start looking around for a wireless connection. The meeting host suggests an SSID. I attach to the network and get directed to a captive portal with an ‘I agree’ button. I press the magic button an get a security warning dialogue.
Anyway – it was amusing. After I switched to my admin account and installed the ‘root kit’ service agent and switched back to my normal user, I got blocked anyway. I’m running Windows 7 RC without anti-virus. I guess NAC did what it was supposed to do. It kept my anti-virus free computer off the network.
I’d like someone to build a shim that fakes NAC into thinking I’ve got AV installed. That’d be useful.

>After I switched to my admin account and installed the ‘root kit'^H^H^H^H^H^H^H^Hservice agent...
ReplyDeleteI LOL'd
Matt -
ReplyDeleteThat's what I said to the host in the meeting - 'What's this rootkit thing you're trying to install?'
We've worked together for a decade & are pretty informal, so it at least provided amusement for the meeting.
I am glad to see our NAC system is working – I am always suspicious of System staff when they are on campus.
ReplyDelete:)
Anyway, I’ll throw my two cents in about NAC systems since this post is here. It’s not a magic bullet that will solve any and all security problems, as NAC was often marketed. It helps protect our network from the unaware students who bring laptops to campus expecting access to services – without patching their systems or running any AV. We average 300 to 500 of these laptops a day over which we have no control.
NAC is decent at policy enforcement, allowing me to try to get student machines to comply with system guidelines. It also can be a teaching tool for students who know nothing about keeping their systems even minimally secured.
It will not stop attackers, which is a common misconception. Once logged in and the AV is running, anyone can attack away. Can a dedicated individual figure out how to bypass a NAC system – yes. That person probably is already smart enough to also patch their system. Stop by my office next time and I can show you how.
James
@James -
ReplyDeleteThanks for the comment.
I'm not really pro or anti NAC, but what struck me (and why I wrote this) was that the popup for a good thing (a NAC agent) is really indistinguishable from something bad (malware), and hence an ordinary user is as likely as not to click OK on both.
That's not anything that a NAC vendor or implementer can fix. It's really a problem with the operating system.
Take care.
Thanks Mike.
ReplyDeleteI understood the point you were getting at and didn’t necessarily take the post as anti NAC. I mostly used the post to put my opinion on NAC systems into the blogosphere (which in my humble opinion are uniquely suited to environments like higher ed).
No worries. Back to lurking…